TECHNOLOGY
TunesKit iPhone Unlocker: Best Software to Unlock iPhone
We often utilize a range of passcodes and passwords on our iPhones to protect our most important and sensitive data. Locking your phone prevents anyone from physically accessing private information on your phone, such as private messages and saved credit card information. What would happen if you misplaced your passcode or Apple ID account? When you forgot iPhone passcode, it may cause ” iPhone is disabled” or a locked iPhone. Therefore, in these circumstances, having reliable and effective unlocking solutions is more crucial than ever. TunesKit iPhone Unlocker has emerged as a potential rival in this cutthroat industry, promising to provide a simple and quick way to unlock iPhones without a passcode. We will look into TunesKit iPhone Unlocker’s primary features, installation process, and overall effectiveness in this review.
What Is TunesKit iPhone Unlocker?
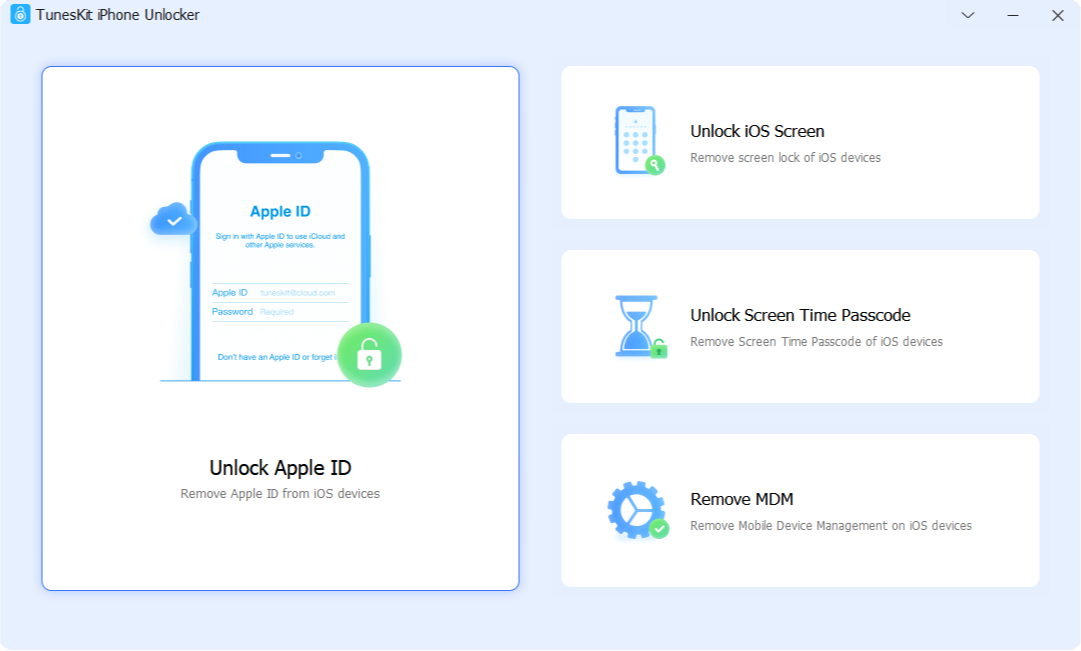
The purpose of TunesKit iPhone Unlocker is to unlock iPhones and remove various types of locks, such as MDM (Mobile Device Management) restrictions, screen passcodes, Apple ID, and screen time. The reputable software company TunesKit, well-known for its multimedia solutions, developed this program in an effort to address the common issue of iPhone lockouts caused by misplaced passcodes, disabled devices, or other security-related problems.
Key Features of TunesKit iPhone Unlocker
- Unlock iOS Screen
One of TunesKit iPhone Unlocker’s most noteworthy features is its ability to unlock several screen passcodes, including 4- and 6-digit passcodes, Touch ID, and Face ID. This ensures that users will never be without a reliable solution in case their biometric systems malfunction or they lose their passcode and can’t access their iPhones.
- Remove Apple ID
TunesKit iPhone Unlocker claims to be able to successfully erase Apple ID from iPhones, allowing users to regain access over their devices. This feature can be especially useful when handling old iPhones or in situations when consumers want to unlink their device from an active Apple ID without needing to provide a password.
- Bypass MDM Restrictions
TunesKit iPhone Unlocker is a dependable MDM uninstallation solution for those who experience constraints related to Mobile Device Management (MDM) on their iPhones. This feature can be very useful for consumers who have bought a secondhand device that is still under MDM management, or for corporate users who want unrestricted access to their work devices.
- Support Various iOS Versions
TunesKit iPhone Unlocker claims to be compatible with a wide range of iOS versions, including the most recent iOS, so users with different iPhone models and software versions can benefit from its unlocking capabilities. This adaptability is crucial because iOS updates regularly, and a reliable unlocking tool must be able to stay up to date with these changes.
How to Use TunesKit iPhone Unlocker
Installing and downloading TunesKit iPhone Unlocker is a simple process. Users can download the program from the official TunesKit website and install it by following the instructions shown on the screen. The application is available for both Mac and Windows operating systems and caters to a broad user base. Next, follow the comprehensive instructions given below to start the unlocking process.
Step 1: Launch the software after the installation is complete. To connect your iPhone to the computer, use a USB cord. If you are unable to recall your screen passcode, select “Unlock iOS Screen”. Click “Start” to get the process started.
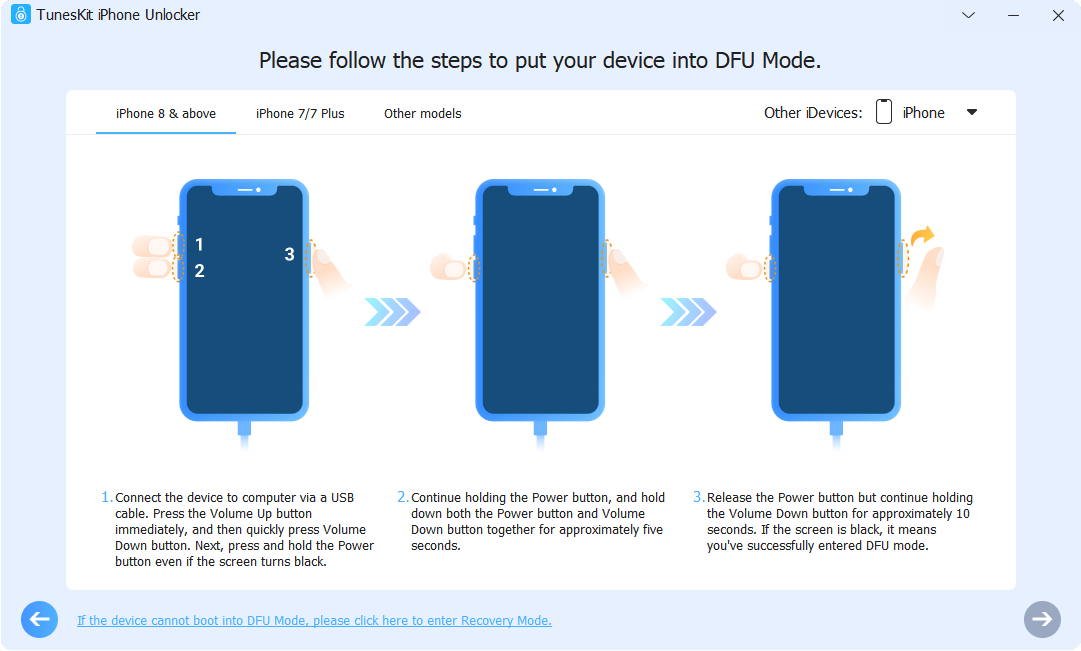
Step 2: Follow the on-screen instructions to put your device into DFU or Recovery Mode. Press the Next button once your iPhone has entered Recovery mode.
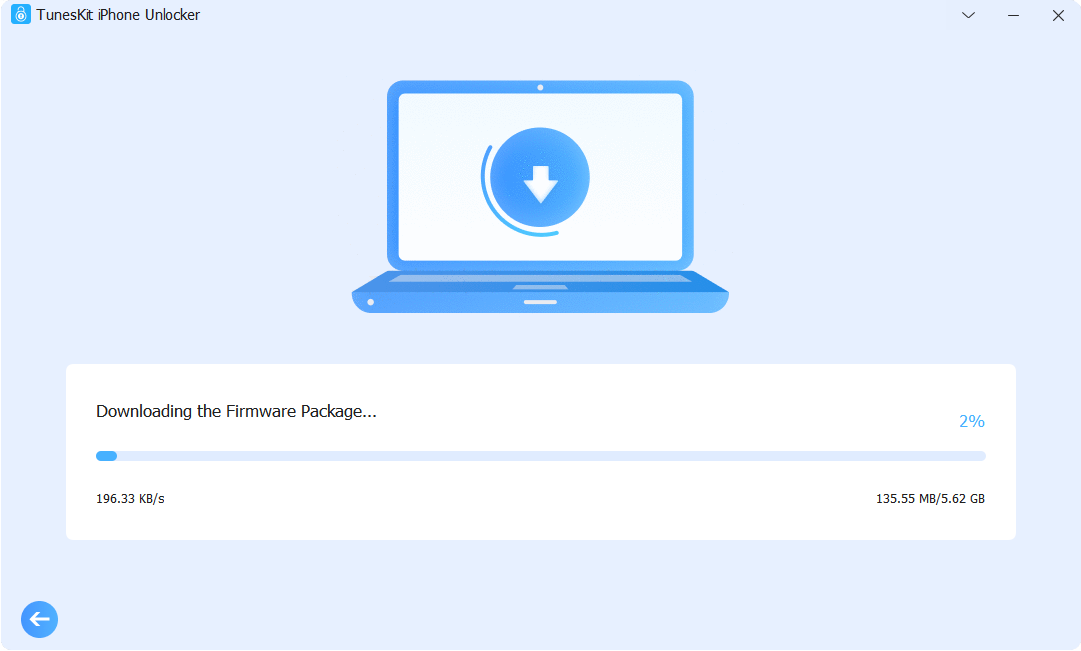
Step 3: TunesKit iPhone Unlocker will download the firmware package required to unlock your screen passcode when it has confirmed the details of your device.
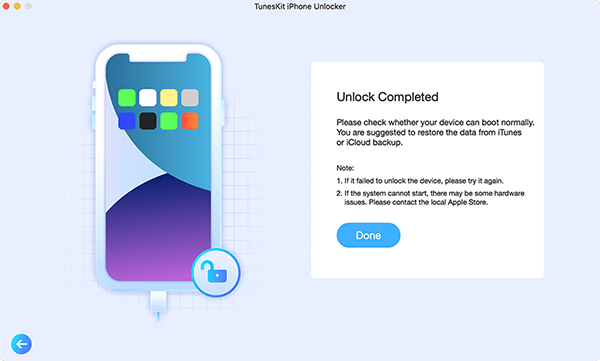
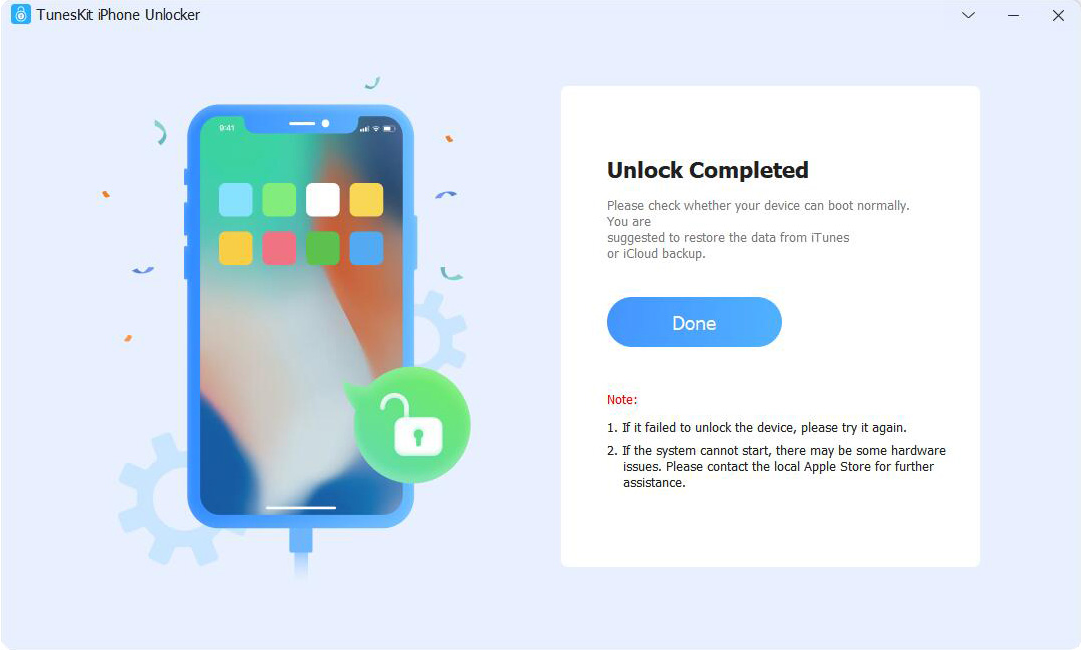
Step 4: When TunesKit finishes the process, it will notify you. You can now unplug the PC and iPhone.
Pros and Cons of TunesKit iPhone Unlocker
- Pros
Versatility: Screen passcodes, Apple IDs, screen time limits, and MDM restrictions are just a few of the iOS device locks that TunesKit iPhone Unlocker can unlock.
User-Friendly Interface: The software’s simple design makes it easy to use even by those without technical background.
Compatibility: Nearly every version of iOS, even iOS 17, is fully compatible with the app.
- Cons
Commercial Software: There is a free trial available for TunesKit iPhone Unlocker, which is a commercial program. To get the entire feature set, users must buy the full edition.
Language Restrictions: This version is only compatible with English.
Conclusion
In summary, TunesKit iPhone Unlocker markets itself as a dependable solution for people with locked iPhones. With its versatility in handling various lock types, user-friendly interface, and compatibility with numerous iOS versions, it’s a promising option when it comes to phone unlocking tools.
However, users should be mindful of the commercial nature of the program and the potential loss of data throughout the unlocking process. Before using TunesKit iPhone Unlocker, it is recommended that you carefully read the terms and conditions, make a backup of any vital data, and weigh the advantages and disadvantages.
For those searching for a reputable and efficient solution to unlock their iPhones, TunesKit iPhone Unlocker may prove to be a valuable investment if users are informed of the potential drawbacks and take the necessary precautions before beginning the unlocking process.
TECHNOLOGY
Why Trwho.com is a Game-Changer in Online Content Discovery

In today’s digital world, content is everywhere. From articles and videos to podcasts and social media posts, the sheer volume of information can be overwhelming. You might find yourself scrolling endlessly, trying to sift through the noise to discover something truly valuable. Enter Trwho.com—a revolutionary platform designed specifically for those lost in the sea of online content.
Trwho.com simplifies your search for high-quality material tailored to your interests. It’s not just another aggregator; it’s a smart solution that transforms how you interact with information online. Whether you’re a casual reader or a dedicated researcher, Trwho.com promises to make content discovery easier and more enjoyable than ever before. Let’s dive into what makes this site so special!
The Problem of Content Overload
Every day, millions of new articles, videos, and podcasts flood the internet. It’s a relentless wave of information that can feel daunting to navigate.
Users are often bombarded with content that lacks relevance or quality. Finding what truly resonates becomes an exhausting chore rather than an enjoyable experience.
Social media platforms and search engines prioritize trending topics over personalized interests. This leads to endless scrolling without substantial discovery and engagement.
As a result, many individuals miss out on valuable insights buried beneath mountains of irrelevant material. The quest for meaningful content often feels like searching for a needle in a haystack.
This struggle is real and affects everyone—from casual browsers to professionals seeking knowledge. With so much noise around us, it’s easy to feel lost in this digital jungle where quality gets overshadowed by quantity.
Introducing Trwho.com – The Solution to Content Discovery
In a digital landscape overflowing with information, finding the right content can feel like searching for a needle in a haystack. Trwho.com emerges as an innovative beacon amidst this chaos.
This platform reshapes how users discover, engage with, and consume content online. By leveraging advanced algorithms and user preferences, it curates personalized recommendations tailored to individual tastes.
Trwho.com eliminates the frustration of endless scrolling through unrelated articles or videos. Instead, it connects users directly to what matters most to them.
Its intuitive interface ensures that navigating vast amounts of data is simpler than ever before. With Trwho.com, discovering relevant content becomes not just easier but also more enjoyable for everyone involved.
How Trwho.com Works
Trwho.com simplifies content discovery with an intuitive interface designed for ease of use. Users can input their interests, and the platform curates personalized content from various sources.
The algorithm analyzes user preferences in real-time, ensuring that each suggestion is relevant and engaging. This means no more sifting through endless articles or videos; Trwho.com brings the best options to your fingertips.
Additionally, it constantly learns from interactions. As you explore different topics, the recommendations evolve to match your changing tastes.
It also integrates seamlessly with social media platforms, allowing users to share their favorite finds effortlessly. Collaborative features enable friends and colleagues to discover content together as well.
This innovative approach transforms how we consume information online, making it a breeze to stay informed without feeling overwhelmed by choices.
Features and Benefits of Trwho.com
Trwho.com offers a streamlined approach to content discovery that sets it apart from traditional platforms. Its intelligent algorithm curates personalized recommendations based on user preferences, saving time and effort.
Users can explore a vast array of topics tailored to their interests. Whether it’s trending news or niche blogs, Trwho.com ensures relevant content is just a click away.
The platform’s intuitive interface makes navigation effortless. With easy-to-use filters, finding specific articles becomes simple and quick.
Another standout feature is the community engagement aspect. Users can share insights on discovered content, enriching the overall experience through collaborative learning.
Notifications keep users updated with fresh content without feeling overwhelmed. This balance enhances satisfaction while minimizing information overload, allowing for focused exploration in an age where distractions abound.
Why Users are Raving About Trwho.com
Users are buzzing about Trwho.com for a variety of compelling reasons. The platform simplifies the often overwhelming task of finding quality content online. With just a few clicks, users can discover tailored articles and videos that resonate with their interests.
The intuitive interface is another highlight. People appreciate how easy it is to navigate through endless streams of information without feeling lost. This streamlined approach saves time and frustration.
Moreover, Trwho.com employs advanced algorithms that learn from user preferences, providing increasingly relevant recommendations over time. Users love this personalized touch, which makes each visit feel unique and engaging.
Community features also play a significant role in its popularity. Users can share insights and discuss findings within the platform, creating an interactive experience that fosters connection among like-minded individuals.
Success Stories from Trwho.com Users
Many users have found their content journey transformed through Trwho.com. For instance, a small business owner discovered relevant articles and insights that helped them tailor their marketing strategy effectively. The result? A noticeable increase in customer engagement and sales.
Another user, a freelance writer, shared how the platform streamlined their research process. With curated content suggestions, they could focus more on writing rather than sifting through endless information online. This boost in productivity led to timely submissions and happier clients.
Educators also praise Trwho.com for finding valuable resources quickly. They’ve enhanced lesson plans using tailored content that resonates with students’ interests.
These stories highlight just how powerful effective content discovery can be when it’s done right. Users are not only saving time but unlocking new opportunities across various fields thanks to Trwho.com’s innovative approach.
The Future of Content Discovery with Trwho.com
As we look ahead, the landscape of content discovery is set to evolve significantly with Trwho.com at the forefront. This platform is designed to streamline how users find relevant and engaging material across various niches.
With advancements in AI and machine learning, Trwho.com will harness these technologies to personalize user experiences even further. Imagine a tool that not only understands your interests but anticipates what you might want next.
The integration of social sharing features promises a more collaborative approach to discovering content. Users can easily share their finds or seek recommendations from friends, creating a vibrant community around shared interests.
Moreover, as new formats like video and interactive media gain traction, Trwho.com adapts accordingly. It ensures that users are always connected with the latest trends while enjoying diverse types of content tailored just for them.
Conclusion
The rise of digital content has transformed how we consume information. But this shift hasn’t come without its challenges. With the internet flooded with articles, videos, and posts, users often feel overwhelmed. That’s where trwho.com steps in as a beacon of clarity amidst the chaos.
Trwho.com is designed to simplify your online experience. It curates content based on your interests and preferences, ensuring that you find what truly matters to you without sifting through endless options.
How does it work? Trwho.com employs advanced algorithms and user-friendly features that tailor recommendations specifically for each user. The platform learns from your interactions and continuously refines its suggestions, making every visit more personalized than the last.
One of the standout features of trwho.com is its intuitive interface. Users can easily navigate through categories or use powerful filters to hone in on specific topics. This level of customization enhances engagement while saving time—an invaluable benefit in today’s fast-paced world.
Users have been quick to share their enthusiasm about trwho.com. Many appreciate not only how seamlessly it fits into their daily routines but also how effectively it uncovers hidden gems they might otherwise miss. Testimonials highlight enhanced discovery experiences that keep them coming back for more.
Success stories abound within the community surrounding trwho.com. From bloggers finding inspiration for new posts to professionals discovering industry insights, users report meaningful changes in their content consumption habits—and overall satisfaction levels are high.
Looking ahead, it’s clear that platforms like trwho.com will shape the future landscape of content discovery even further. As technology evolves and our needs adapt, innovations will continue enhancing personalization efforts across various niches, making it easier than ever for individuals to connect with relevant material effortlessly.
As we embrace this dynamic era of online exploration together with tools like trwho.com at our fingertips, navigating through a sea of information becomes less daunting—transforming our relationship with digital content into one that’s enriching rather than overwhelming.
TECHNOLOGY
Prizmatem: A New Wave of Creative Tech Innovation

In the ever-evolving digital landscape, new terms often emerge that symbolize transformation and forward-thinking. One such rising concept is Prizmatem—a word that’s beginning to make waves across creative and tech spaces. Though unfamiliar to many, Prizmatems is fast becoming a powerful term representing multidimensional design, digital storytelling, and innovation that blurs the line between technology and art.
Understanding the Essence of Prizmatem
So, what exactly is Prizmatem? At its core, it is a fusion of visual artistry, interactive technology, and modern design philosophy. The word itself evokes imagery of prisms—objects that split light into a spectrum. In the same way, Prizmatem symbolizes ideas that branch into multiple directions, offering diverse solutions, layered meanings, and immersive experiences.
Prizmatems is not limited to a single industry. It can be found in user interface design, digital media, branding, gaming, and even architecture. Wherever there’s a need to create engaging, multi-sensory experiences, Prizmatems can take center stage.
The Origins and Inspiration Behind Prizmatem
The inspiration behind Prizmatem is drawn from the natural world and its interaction with light. Much like a prism transforms white light into vibrant colors, Prizmatems aims to transform simple content into vibrant, layered experiences. It’s inspired by the idea that every piece of information or design can have multiple angles, perspectives, and interpretations.
The term may be new, but the philosophy behind it isn’t. Designers, developers, and creatives have long searched for ways to create richer digital experiences. Prizmatems simply gives this pursuit a name—a creative code that blends emotion, innovation, and interaction.
Key Elements of the Prizmatem Approach
To understand how Prizmatem works in practice, let’s break down its major components:
1. Multilayered Design
Prizmatems uses depth, transparency, and layering to create designs that feel alive and three-dimensional. This is often achieved through clever use of gradients, shadows, and animation.
2. Responsive Interactivity
A crucial aspect of Prizmatems is user interaction. The experience changes and responds to movement, clicks, scrolling, or even environmental factors like time or weather in smart interfaces.
3. Tech Meets Aesthetics
Prizmatem merges cutting-edge technologies like WebGL, motion graphics, AR/VR, and AI-driven personalization to provide a visually impressive and emotionally resonant experience.
4. Color as Communication
Colors aren’t just decorative in Prizmatem—they are used to convey emotion, direct user attention, and highlight transitions. Think bold spectrums, glowing edges, and light-inspired animations.
Where Prizmatem Is Making an Impact
This emerging concept is versatile, and its influence is already visible in several domains:
Digital Experiences
Many websites and mobile apps now feature immersive animations, 3D effects, and reactive visuals—a clear nod to the Prizmatems philosophy.
Branding and Identity Design
Companies are exploring new visual identities by moving beyond static logos. Animated brand elements, color-shifting palettes, and reactive typefaces all speak to a Prizmatem-inspired approach.
Gaming and Virtual Worlds
Games are a natural playground for Prizmatems. From sci-fi landscapes to customizable avatars, this concept allows for deeper immersion and storytelling.
NFTs and Digital Art
Digital art creators are using Prizmatem-style visuals in interactive NFTs, which change appearance based on user interaction, time of day, or device used.
Benefits of Adopting Prizmatem
Integrating Prizmatem principles can unlock numerous advantages:
-
Enhanced User Engagement: Interactivity and visual appeal keep users interested and coming back.
-
Greater Emotional Impact: Thoughtful design and motion can stir curiosity, excitement, or calm—depending on intent.
-
Future-Proof Branding: Using layered design and motion-driven visuals positions your brand as innovative and forward-looking.
-
Creative Freedom: Prizmatems gives artists and designers more freedom to break the grid and explore new expressions.
Challenges of Using Prizmatem
While Prizmatem opens new creative doors, it’s not without its challenges:
-
Performance Load: Heavy visuals and animations can slow down websites or apps if not optimized correctly.
-
Accessibility Concerns: Some visual elements may make it harder for users with disabilities to navigate or understand content.
Tips for Embracing Prizmatem in Your Projects
Ready to bring a Prizmatem aesthetic to your next creative project? Here are some actionable steps:
-
Start with a Story – Design should support a narrative. Think about how color, shape, and movement can help tell your story.
-
Experiment with Layering – Use transparency, overlapping shapes, and shadows to add visual depth.
-
Use Motion Strategically – Add transitions and hover effects that serve a purpose, such as guiding users or enhancing comprehension.
-
Optimize for Performance – Compress graphics, use lazy loading, and test on multiple devices.
-
Prioritize Accessibility – Ensure your content is readable, with alt text, contrast adjustments, and keyboard navigation.
The Future of Prizmatem
As digital expectations continue to evolve, Prizmatem is set to grow in relevance. It’s more than a style—it’s a design mindset for the modern digital world. We are moving into an era where users crave experiences that feel personal, immersive, and visually captivating. Prizmatems satisfies this demand by offering an approach where tech meets creativity at every level.
From next-gen apps to interactive educational tools, the possibilities with Prizmatems are vast and promising.
Final Thoughts
Prizmatem represents a bold step into the future of design and digital expression. It encourages us to think beyond flat visuals and static layouts, inspiring experiences that engage all senses and spark curiosity. For businesses, creatives, and technologists alike, understanding and embracing the principles of Prizmatems could open doors to richer storytelling, deeper engagement, and boundary-pushing innovation.
As we look ahead, one thing is certain: Prizmatems is not just a buzzword—it’s a vision of what digital creativity can become.
TECHNOLOGY
Quartist: The New Age of Digital Art and Creative Expression

In today’s digitally-driven world, the creative landscape is constantly shifting. At the forefront of this evolution is a new kind of artist — the quartist. A blend of “quality” and “artist,” the term defines a modern creator who blends high-caliber craftsmanship with forward-thinking digital tools. Quartists are not bound by traditional brushes and canvases; instead, they use technology, innovation, and artistic insight to push the boundaries of expression.
Who is a Quartist?
A quartist is more than just a digital designer. They are visual storytellers, tech-savvy creators, and detail-driven innovators who prioritize quality in both process and output. Unlike casual creators, a quartists approaches their work with intentionality, constantly learning and adapting to new media forms.
Whether working in graphic design, animation, virtual reality, or digital illustration, quartists are focused on crafting meaningful, polished, and impactful content.
The Core Principles of a Quartist
To better understand the essence of a quartist, let’s break down the qualities that define this modern creative identity:
1. Quality-First Approach
A quartists does not settle for “good enough.” Their artwork is refined, thoughtful, and technically sound. Every detail — from linework to lighting — is approached with precision.
2. Embracing Digital Tools
Modern quartists often use tools like Adobe Illustrator, Procreate, Blender, and even AI-assisted platforms to enhance their work. Yet, tools never replace creativity — they elevate it.
3. Continuous Innovation
A quartists constantly evolves, learning new techniques and experimenting with formats like AR, VR, NFTs, and generative art to stay ahead in the ever-changing creative space.
How the Quartist is Redefining Art
The digital age has given rise to a new artistic revolution. Quartists play a key role in this shift by challenging conventional methods and introducing new styles and standards.
Digital Platforms, Real-World Impact
Through platforms like Instagram, Behance, and Foundation, quartists gain global visibility. Their work is exhibited not just in galleries but also in virtual showrooms, games, and metaverse spaces.
NFTs and Blockchain for Authenticity
By minting their work as NFTs, quartists can authenticate and sell original art without relying on traditional art dealers. This decentralization of the art market gives more power and recognition to independent creators.
The Tools Behind the Quartist’s Craft
The quartist toolkit is diverse, and it keeps expanding. While some may use 3D modeling software, others rely on digital painting tools or code-based creative programs.
Here are some favorites among today’s quartists:
-
Procreate – for digital sketching and illustration
-
Blender – for 3D animation and modeling
-
Midjourney & DALL·E – for AI-generated concept development
-
Figma & Adobe XD – for interface and UX art
-
Unity & Unreal Engine – for immersive, interactive art installations
The key is not the tool, but how it’s used. A true quartists knows how to make technology serve the vision — not the other way around.
Becoming a Quartist: Skills and Mindset
Becoming a quartist doesn’t require formal degrees, but it demands dedication, self-discipline, and a passion for digital artistry. Here are a few steps that aspiring quartists can follow:
Learn the Foundations
Understanding color theory, composition, and visual storytelling is essential, no matter the medium.
Master the Digital Tools
Pick a primary platform — whether it’s Photoshop or Blender — and practice regularly. Tutorials, courses, and personal projects help build fluency.
Build a Portfolio
A quartist’s value lies in their work. Document your projects, display them online, and highlight the process behind each piece.
Stay Curious
The creative world evolves quickly. Quartists must embrace lifelong learning and be open to exploring new tools, formats, and concepts.
The Quartists Community: Collaboration Over Competition
Unlike the solitary image of the traditional artist, modern quartists thrive in communities. They connect through Discord channels, Twitter art spaces, and Reddit forums to share feedback, collaborate on projects, and even host digital exhibitions.
This open culture has created a powerful movement where artists from different parts of the world inspire and elevate one another. A quartist isn’t just a creator — they’re part of a collective revolution.
Challenges Faced by Quartists
The quartist path is inspiring, but not without hurdles. These include:
-
Oversaturation of digital platforms, making it harder to stand out.
-
Plagiarism and theft, especially for digital art shared online.
-
Mental fatigue from the pressure to create constantly and keep up with trends.
-
Monetization difficulties despite high-quality work.
Still, quartists remain resilient. By continuing to innovate and connect with their audiences, many find both fulfillment and success in their creative careers.
The Future of the Quartist Movement
The future looks promising for quartists. With advancements in AI, blockchain, and immersive technology, new opportunities will continue to arise.
From art therapy apps powered by machine learning to generative exhibitions in the metaverse, quartists will play a key role in shaping how we define and experience art in the next decade.
These creators are not just following trends — they are setting them. Their influence extends beyond aesthetics to the core of cultural and technological transformation.
Final Thoughts: Why Quartist Matters Now More Than Ever
In a digital world often flooded with fleeting content, the quartist emerges as a voice of intention, innovation, and excellence. By blending technology with creativity, these artists are redefining what it means to be a creator in the 21st century.
Whether you’re an aspiring artist, a creative professional, or simply an art enthusiast, keeping an eye on the quartists movement means staying in tune with the next wave of digital transformation.
-

 GENERAL1 year ago
GENERAL1 year agoDiscovering the Artistic Brilliance of Derpixon: A Deep Dive into their Animation and Illustration
-

 FASHION2 years ago
FASHION2 years agoThe Many Faces of “λιβαισ”: A Comprehensive Guide to its Symbolism in Different Cultures
-

 Posts2 years ago
Posts2 years agoSiegel, Cooper & Co.
-

 Lifestyle2 years ago
Lifestyle2 years agoPurenudism.com: Unveiling the Beauty of Naturist Lifestyle
-

 Lifestyle1 year ago
Lifestyle1 year agoBaddieHub: Unleashing Confidence and Style in the Ultimate Gathering Spot for the Baddie Lifestyle
-

 HEALTH1 year ago
HEALTH1 year agoTransformative Health Solutions: Unveiling the Breakthroughs of 10x Health
-

 Entertainment2 years ago
Entertainment2 years agoGeekzilla Podcast: Navigating the World of Pop Culture, Gaming, and Tech
-

 Lifestyle10 months ago
Lifestyle10 months agoSandra orlow: Unraveling the Story of an Iconic Figure
